Your Partner in Cyberdefense!
The Cyber Defense Matrix (CDM) is a powerful framework designed to help organizations manage and improve their cybersecurity posture by categorizing and aligning security capabilities across five critical functions: Identify, Protect, Detect, Respond, and Recover. Developed to bridge gaps between business and technical teams, the matrix ensures a balanced and comprehensive approach to cybersecurity, helping organizations address every stage of the threat lifecycle while maintaining operational resilience. By mapping existing controls to the matrix, businesses can ensure they have appropriate defenses in place across all critical areas, rather than focusing solely on one aspect of security.
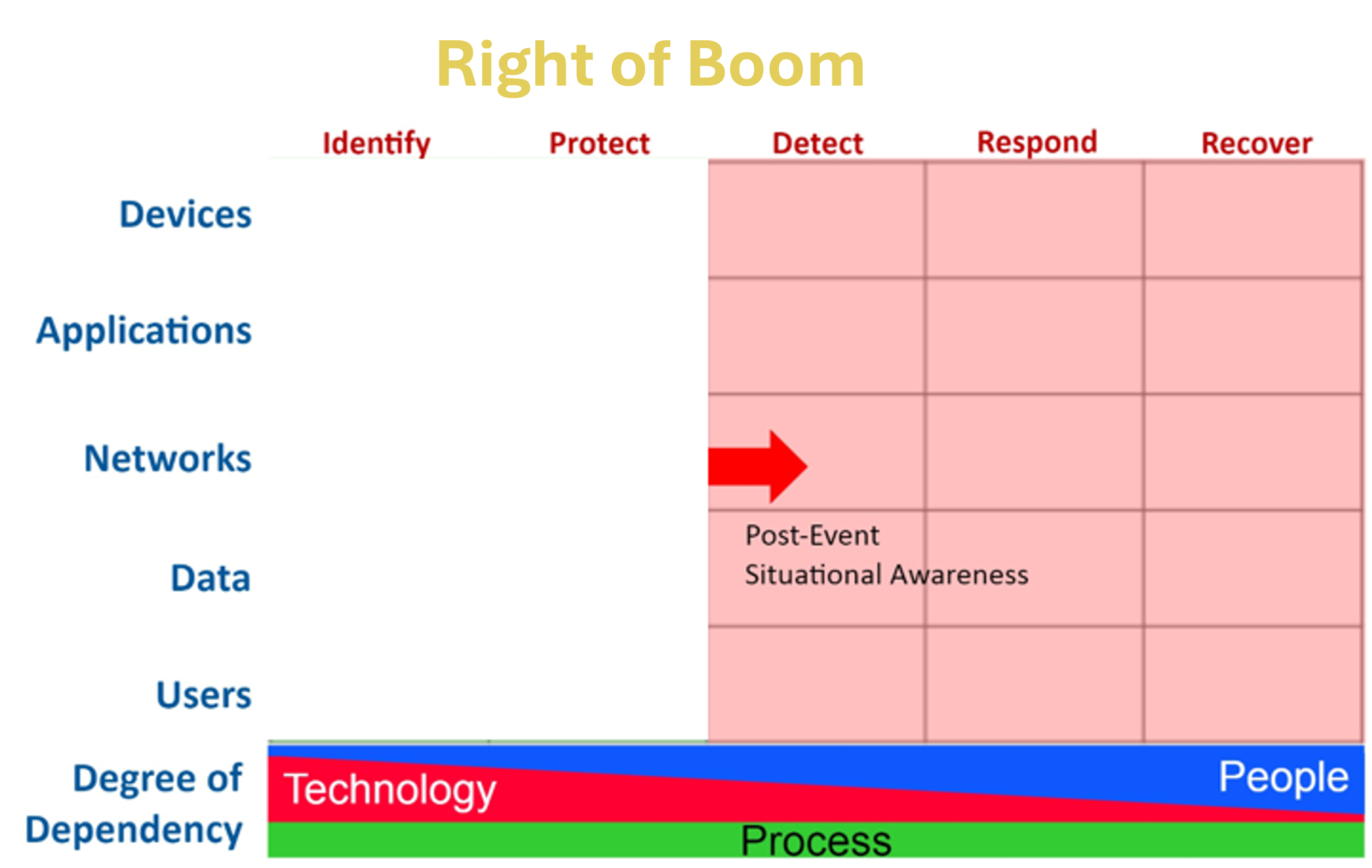
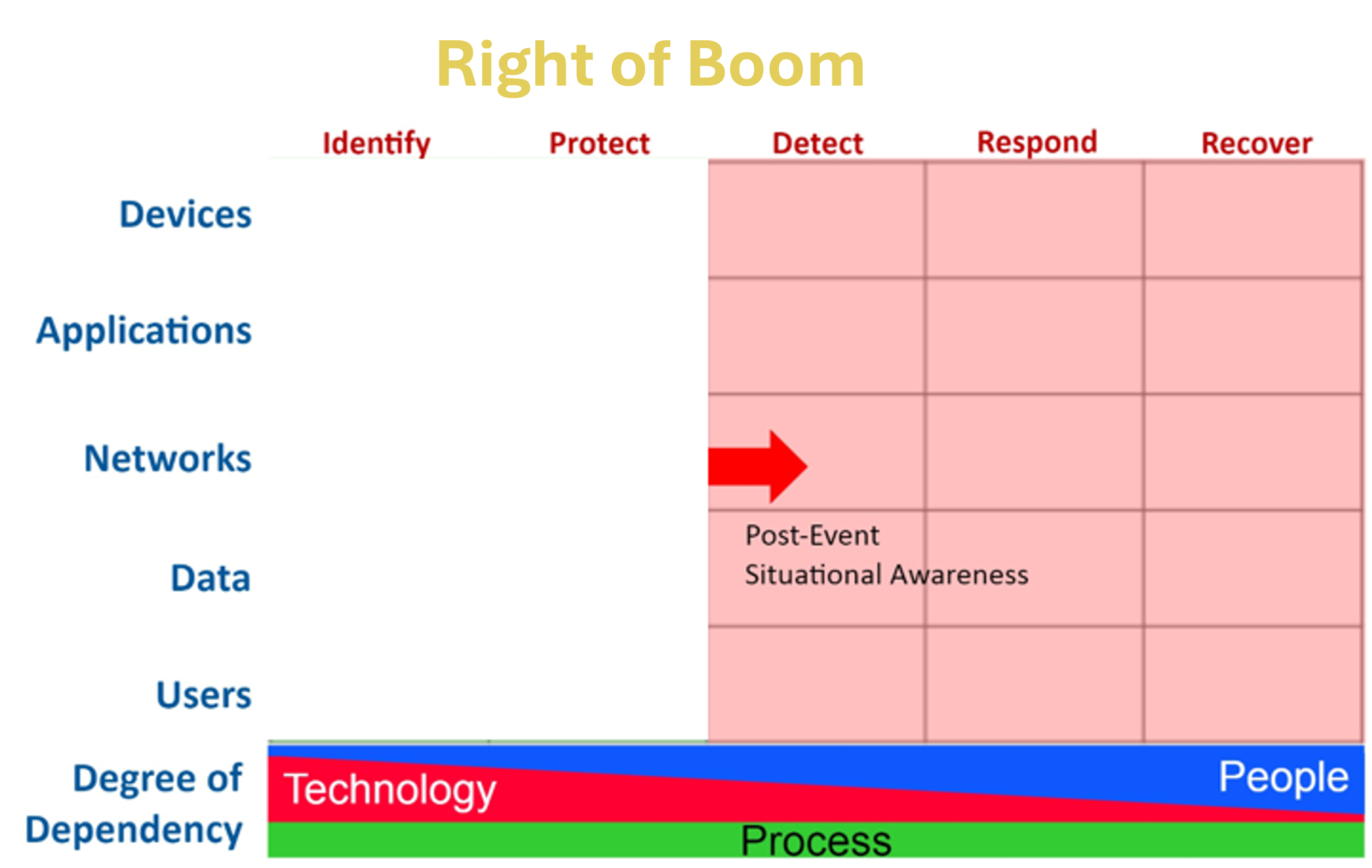
The Cyber Defense Matrix is built based on the NIST Cybersecurity Framework and maps:
– The five operational functions: identify, protect, detect, respond, recover
– The five asset classes: devices, applications, networks, data, users
– The degree of dependency on people, technology, and process.
From left to right, the identify and protect columns speak to structural awareness. On the right, situational awareness takes over in the detect, respond, and recover columns.
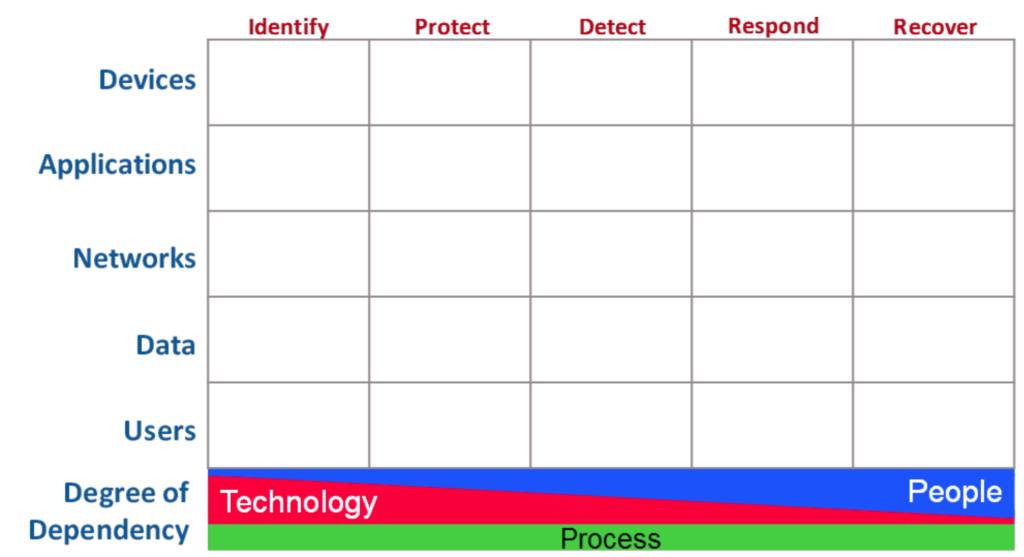
The bottom of the Cyber Defense Matrix template includes the degree of dependency on People, Process, and Technology at different stages of a cybersecurity event. It shows how Technology plays a major role in Identify and Protect, while dependency on People grows as it moves to Detect and Respond. Process remains at a consistent level of dependency.

The bottom of the Cyber Defense Matrix template includes the degree of dependency on People, Process, and Technology. It shows how Technology plays a major role in Identify and Protect, while dependency on People grows as it moves to Detect and Respond. Process remains at a consistent level of dependency.
Here Comes the BOOM!
It is important to note that the latest cybersecurity technologies do not automatically improve your security posture. There is a common misconception that the matrix means that more technology means better security. But an overemphasis on technology can create more gaps. That is why the matrix includes how people, processes, and technology are needed for a comprehensive cybersecurity strategy.
The human component will always be important. Employees play a significant role in maintaining security measures, which the matrix emphasizes. Finally, keep in mind that the Cyber Defense Matrix is not a static framework. Cyber threats are constantly evolving, and so should your strategy. A cybersecurity event is always lurking in the future.
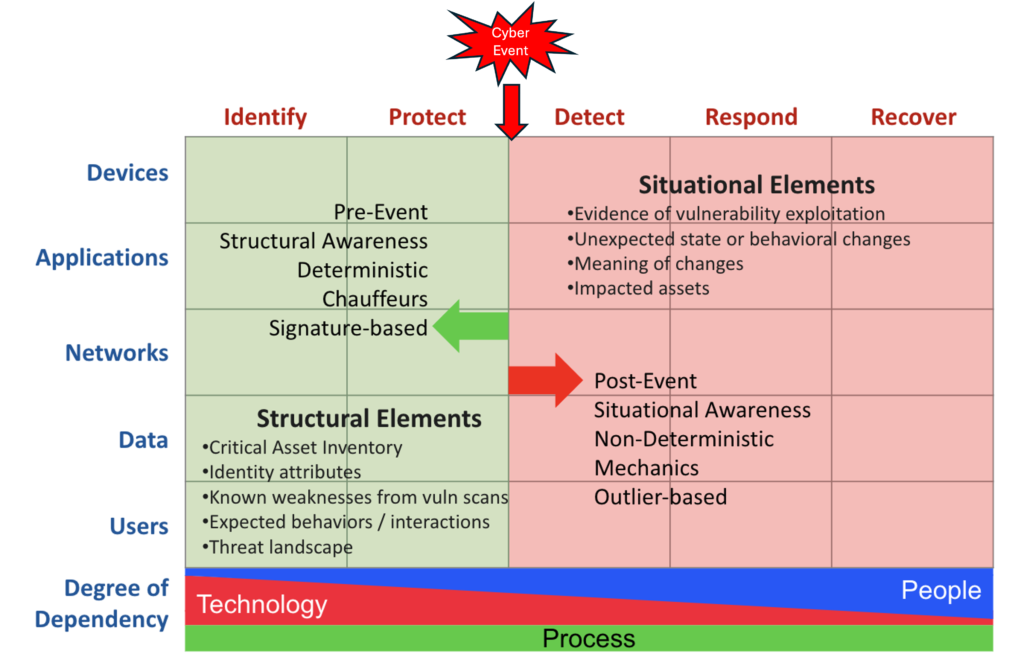
The “BOOM” represents a cyber incident. To Summarize, “Left of Boom” focuses on prevention, while “Right of Boom” deals with response and recovery.
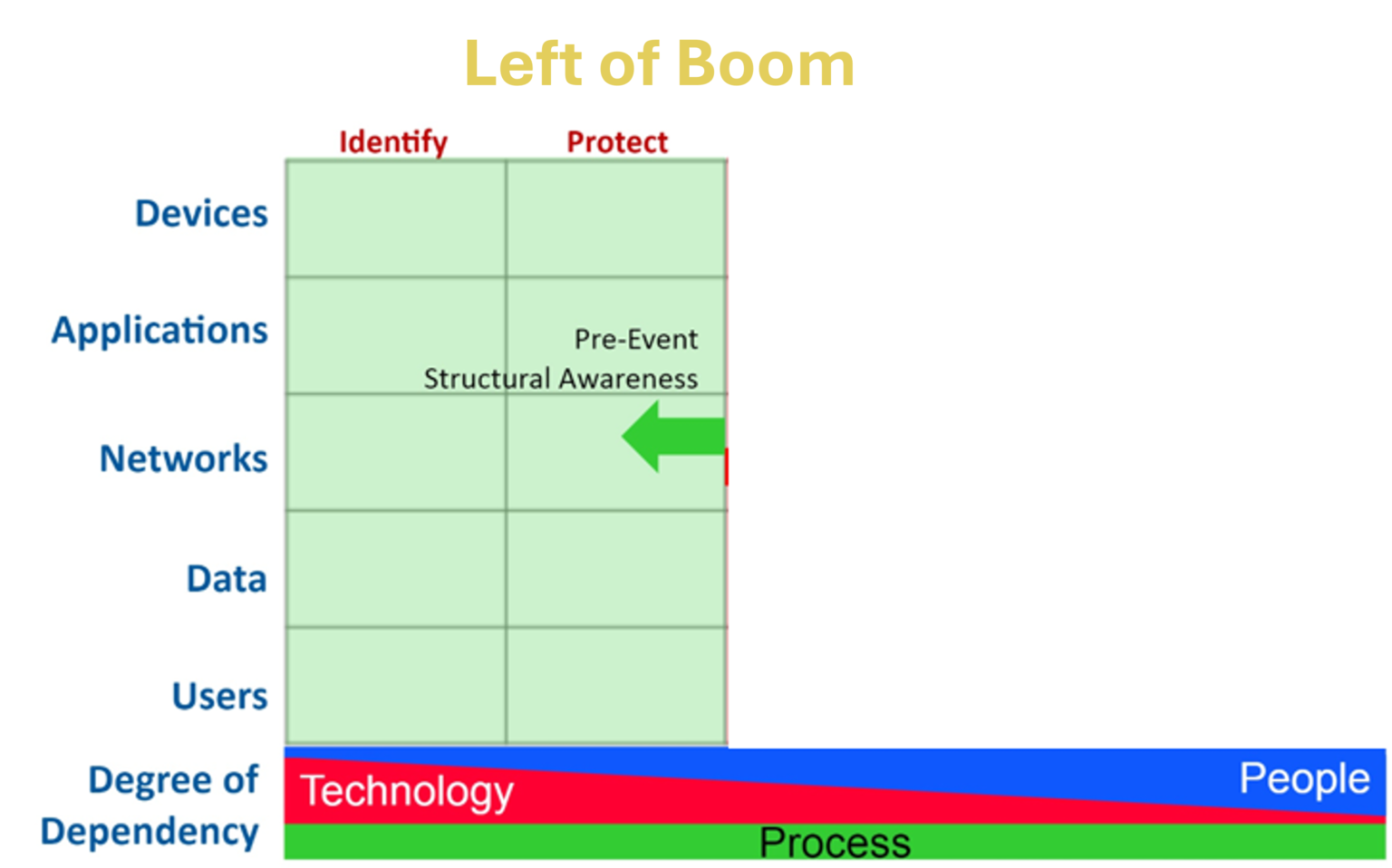
Left of Boom = Prevention and Preparedness
Actions taken before an attack occurs.
Examples include:
- Implementing security controls and best practices.
- Conducting vulnerability assessments.
- Educating employees about security awareness.
- Regularly updating software and patching vulnerabilities
Right of Boom = Response and Recovery
Actions taken after an attack occurs.
Examples include:
- Investigating the breach.
- Containing and mitigating damage.
- Restoring affected systems.
- Communicating with stakeholders

As we move from left to right (before and after the BOOM), the degree of dependency on technology is INVERSE with the degree of dependency on people. Our dependency on process, however, remains constant throughout all five functions. This continuum helps us pinpoint where we rely on which resources.
The Halcyon Cyberworks Top 5
In a world where cyber threats grow more sophisticated by the day, choosing the right cybersecurity partner is crucial to protecting your business and staying ahead of potential risks. At Halcyon Cyberworks, we combine cutting-edge technology, tailored solutions, and decades of expertise to deliver unparalleled value. Here are five compelling reasons why Halcyon Cyberworks is the trusted choice for your cybersecurity needs.
#1 - Cybersecurity ≠ Cyber Resilience
Traditional cybersecurity strategies focus primarily on prevention—blocking attacks before they penetrate an organization’s defenses. However, the reality is that determined adversaries often find ways to exploit vulnerabilities and bypass these safeguards. That’s why cyber resilience is the critical differentiator between businesses that merely survive and those that thrive after a cyberattack. Cyber resilience goes beyond prevention, embracing a holistic approach that minimizes the impact of successful attacks while ensuring business continuity, protecting critical data, and maintaining operational integrity. It’s not just about deploying a collection of security tools—it’s about creating a comprehensive strategy that includes:
- Proactive Threat Hunting: Actively identifying hidden threats before they cause damage.
- Rapid Incident Response: Utilizing well-defined procedures and automated tools to quickly contain and eradicate threats.
- Robust Data Backup and Recovery: Ensuring critical data is restored swiftly and efficiently after a disruption.
- Business Continuity and Disaster Recovery Planning: Maintaining essential operations during and after an incident.
At our Halcyon Cyberworks, we take this holistic approach, aligning our solutions with the NIST Cybersecurity Framework and the Cyber Defense Matrix (CDM) to provide a structured, comprehensive defense. Powered by advanced automation, intelligent AI tools, and proven frameworks, we secure your most critical assets and keep your business operational—even in the face of the unexpected.
We’re not just a vendor of cybersecurity tools—we’re your strategic partner, dedicated to helping your business adapt, evolve, and thrive. With our support, you can confidently operate knowing your organization is prepared to defend, respond, recover, and continuously improve, no matter the challenges. Together, we’ll build a business that’s not just secure—but operationally resilient.
#2 - Intelligent Automation: Pay for Automation, Not Labor
In today’s fast-evolving threat landscape, manual security operations are no longer enough. They’re costly, inefficient, and prone to human error. That’s why we embrace the principle of “Pay for Automation, Not Labor”—a philosophy that prioritizes efficiency, cost savings, and resilience through AI-enabled and automation-first cybersecurity solutions.
Our platform leverages advanced tools like SOAR, XDRaaS, and Workflow Automation to streamline operations, enhance efficiency, and minimize manual intervention. These tools actively identify, manage, and neutralize threats with minimal human oversight, allowing your team to focus on what matters most—running your business.
The Cyber Defense Matrix (CDM) provides a structured lens through which to view this value. It divides cybersecurity efforts into two phases: Left of Boom (proactive measures before an incident) and Right of Boom (reactive efforts after an incident).
Left of Boom: Proactive Automation
In the pre-incident phase, automation drives proactive measures designed to prevent or minimize the impact of attacks. This includes continuous monitoring, vulnerability scanning, threat intelligence analysis, and automated incident response actions. Investing in automation during this phase significantly reduces operational burdens and costs, ensuring potential issues are identified and mitigated before they escalate.
Right of Boom: Expert Intervention with Minimal Labor
When an incident does occur, the focus shifts to reactive efforts. While some manual intervention is necessary, relying solely on manual labor in this phase can be expensive, time-consuming, and inefficient. With our approach, automation significantly reduces the extent of manual response required, ensuring rapid containment, recovery, and minimal downtime.
Why Choose Us?
Our AI-driven automation tools do the heavy lifting both before and after incidents, ensuring you’re not paying for inefficiencies but benefiting from proactive prevention and expert, streamlined response. Here’s how we make a difference:
- Cost Efficiency: Automation minimizes reliance on manual labor, reducing operational overhead and maximizing ROI.
- Rapid Threat Response: Automated tools detect and neutralize threats faster than any manual process could achieve.
- Operational Focus: By handling the complexities of cybersecurity, we free up your team to concentrate on core business objectives.
- Error Reduction: Automation eliminates human error in critical tasks, improving overall security posture.
This isn’t just a strategy—it’s a smarter, value-driven approach to cybersecurity. By prioritizing automation in the Left of Boom phase, we reduce your reliance on costly manual intervention in the Right of Boom phase, ensuring a more efficient, resilient, and cost-effective security posture.
With us, you're not just investing in cybersecurity—you’re investing in a future-proof approach that prioritizes automation, efficiency, and resilience.
#3 - Tailored Solutions for Comprehensive Protection
At our core, we believe that cybersecurity is not a one-size-fits-all solution. Every business and organization has unique security needs, risk profiles, and compliance challenges. That’s why we take a value-driven approach, focusing on tailoring our services to address your specific vulnerabilities, risks, and operational goals.
Understanding Your Unique Needs
Our process begins with a thorough cybersecurity assessment, utilizing industry-leading frameworks like the NIST Cybersecurity Framework and our proprietary Cyber Resilience Questionnaire. These tools provide deep insights into your current cybersecurity maturity and resilience posture, helping us identify gaps and prioritize critical improvements.
We then design customized strategies and service packages aligned with your specific needs and budget, ensuring you receive maximum protection without unnecessary costs. “It’s not about price—it’s about value.” Our approach quantifies the potential cost of inaction and demonstrates how our services mitigate risks, providing you with a clear return on investment.
Comprehensive Managed Security Services
To achieve true cyber resilience, organizations need a unified, integrated approach to security that simplifies management and reduces the burden on internal IT teams. Our suite of services provides end-to-end protection across all attack vectors, ensuring no vulnerability is overlooked.
- XDRaaS (Extended Detection and Response as a Service): Delivers proactive threat detection and response across endpoints, networks, and cloud environments, correlating security data to stop advanced threats in real time.
- SOCaaS (Security Operations Center as a Service): Provides 24/7 monitoring, incident response, and threat hunting by experienced analysts to ensure threats are neutralized before they escalate.
- GRCaaS (Governance, Risk, and Compliance as a Service): Simplifies compliance with regulatory standards, assists with audits, and helps manage organizational risk with expert policy guidance.
- Workflow Automation: Streamlines operations, reduces manual intervention, and eliminates inefficiencies in threat response and management.
- Phishing Awareness and Cybersecurity Training: Empowers your team to recognize and respond to social engineering attacks, one of the most common and damaging threat vectors.
- vCISO Services: Access to experienced virtual Chief Information Security Officers to provide strategic guidance and ensure your cybersecurity aligns with business goals.
- Advanced Protection Tools: Including DNS filtering, MFA & SSO, email protection, password vaults, and one year of free log storage for hot data.
- Incident Response and Recovery: Rapid containment and eradication of threats to minimize downtime and operational impact.
With this robust portfolio of services, we deliver enterprise-grade protection that is flexible, scalable, and designed to adapt to your organization's evolving needs.
Tailored for SMBs and Government Agencies
We understand that small and medium-sized businesses (SMBs) and government organizations face unique challenges, including limited budgets, resource constraints, and stringent compliance requirements. Our solutions are specifically designed to address these needs:
- For SMBs: We provide enterprise-level security at a price point that fits your budget, ensuring your business remains competitive and trusted by customers.
- For Government Agencies: Our services are built to meet stringent regulatory requirements while protecting sensitive citizen data from evolving threats.
Why Partner with Us?
When you partner with us, you’re not just purchasing cybersecurity tools—you’re gaining a strategic partner dedicated to helping you achieve unbreakable cyber resilience. We focus on providing comprehensive, tailored, and scalable solutions to ensure your business or organization is prepared to defend, respond, and recover in today’s threat landscape.
With our support, you can operate with confidence, knowing your critical assets are protected by proven frameworks, advanced automation, and a team of experts committed to your success. Whether you're an SMB or a government agency, we deliver solutions that go beyond protection to provide peace of mind and long-term value.
#4 - Expertise and Experience Across the Cyber Domain
No two organizations are the same, and we understand the diverse challenges faced by small and medium-sized businesses (SMBs) and government agencies alike. Whether you're safeguarding sensitive citizen data, ensuring regulatory compliance, or securing customer trust, we specialize in delivering tailored cybersecurity solutions that address your unique pain points. With years of experience and a customer-first philosophy, our Halcyon Cyberworks offers a comprehensive range of services that adapt to your size, industry, and risk profile. Our expertise doesn’t stop at tools—we build solutions that evolve with your business to ensure you’re always one step ahead of emerging threats.
Local Expertise, Global Perspective
As a DMV-based MSSP, we bring unparalleled insight into the security challenges specific to the region. Whether it's compliance requirements for government contractors, security concerns for healthcare providers, or risks faced by industries prevalent in the DMV area, we possess the local knowledge to address your needs effectively.
Our regional expertise is further strengthened by a global perspective, leveraging worldwide threat intelligence and best practices to deliver advanced protection against the latest cyber threats. This dual approach ensures that we offer comprehensive, context-aware security solutions tailored to your specific environment.
Why Choose Us?
- Customer-Centric Approach: We work closely with your team to design solutions that are precisely aligned with your needs, eliminating unnecessary costs and ensuring maximum efficiency.
- Proven Expertise: Backed by years of experience and a focus on evolving threats, our team delivers solutions that keep you ahead of adversaries.
- Scalable, Tailored Solutions: Whether you’re a growing SMB or a government agency with complex requirements, our services adapt as you do, ensuring security never becomes a limitation.
- Local Understanding, Global Vision: By combining regional insights with global best practices, we ensure your organization is fortified against local and international threats alike.
Conclusion
In today’s rapidly evolving threat landscape, cyber resilience is no longer optional—it’s essential. Organizations that adopt a proactive, automated, and value-driven approach to cybersecurity can significantly reduce risks, minimize the impact of attacks, and ensure business continuity. At Halcyon Cyberworks we provide the expertise, technology, and support necessary to build unbreakable cyber resilience, empowering your business to thrive in the digital age. With us as your partner, you gain more than just protection—you gain confidence and peace of mind.
Halcyon Cyberworks is led by a founder with over a decade of cybersecurity experience and nearly two decades of service to the U.S. government. This background gives us unparalleled insight into protecting critical assets and navigating complex security challenges. Our expertise spans commercial and government sectors, ensuring we’re equipped to handle threats of any scale and complexity. When you partner with us, you gain access to a trusted advisor with a proven track record of success.
#5 - Strategic ROI for Your Business
When it comes to cybersecurity, the decision isn’t about finding the cheapest option—it’s about selecting the right partner to secure your business and ensure its growth. At Halcyon Cyberworks, we prioritize delivering value-driven solutions that address your specific challenges, mitigate risks, and transform your cybersecurity investments into a strategic advantage.
Our approach begins with a tailored assessment, such as the NIST Cybersecurity Framework Quick Assessment, to gain a deep understanding of your current security posture. Using these insights, we design customized solutions that ensure measurable outcomes, including:
- Reduced Downtime: Minimize business disruptions with proactive threat mitigation and rapid recovery strategies.
- Enhanced Compliance: Meet regulatory requirements with ease, avoiding penalties and protecting sensitive data.
- Stronger Security Posture: Safeguard your reputation and critical assets with a defense strategy that evolves with emerging threats.
We firmly believe that “it’s not about price…it’s about value.” By quantifying the potential cost of inaction—such as data breaches, operational downtime, and compliance failures—we demonstrate how our services provide significant ROI. Every dollar you invest in our solutions helps to avoid costly breaches, improve operational efficiency, and strengthen your competitive position in the market.
Why Choose Us?
With Halcyon Cyberworks you’re not just purchasing tools—you’re investing in:
- Peace of Mind: Confidence that your business is protected from evolving cyber threats.
- Operational Resilience: A clear path to maintaining business continuity, even in the face of adversity.
- Strategic Advantage: Turning cybersecurity into a competitive edge, safeguarding your reputation while enabling growth.
By aligning security with business goals, we transform cybersecurity from a cost center into a growth enabler, ensuring your organization is not only protected but also positioned to thrive in the digital age. Let us help you unlock the full potential of your cybersecurity investments and achieve value far beyond price.
Per User Pricing
At Halcyon Cyberworks, we believe in providing transparent, scalable pricing that fits your organization’s unique needs. Our per-user pricing model ensures you only pay for what you use, making it an ideal choice for businesses of any size. This approach offers greater flexibility and predictability compared to traditional flat-rate or per-device pricing, allowing you to scale your cybersecurity services as your organization grows. With Halcyon Cyberworks, you get enterprise-grade protection without the unnecessary costs, delivering exceptional value and peace of mind.
Basic
- Endpoint Protection (EPP)
- AI-Powered SECOPS Platform
- NextGen-SIEM
- Automated Threat Detection
- Automated Incident Response
- Case Management
- DNS Filtering
- MFA, SSO, or Password-less access
- 1 Year Log Cold Storage
Standard
- All of Basic plus:
- AI-Powered SECOPS Platform
- XDRaaS
- NDR
- RMM
- TIP
- Playbooks/Runbooks
- Compliance Dashboard
- Security Assessments & Reporting - QUARTERLY
Premium
- All of Standard plus:
- SOCaaS - Global
- CSPM
- UEBA
- FIM
- Email Security
- GRC, Risk Management & Compliance Support
- Security Assessments & Reporting - MONTHLY
Enterprise
- All of Premium plus:
- GRCaaS
- Cyber Insurance Partnership
- AI-Native Workflow Automation
- Vulnerability & Attack Surface Management
- Cybersecurity Awareness Training
- Security Assessments & Reporting - CONTINUOUS
Need A La Carte Pricing?
Meet the Halcyon Leadership Team
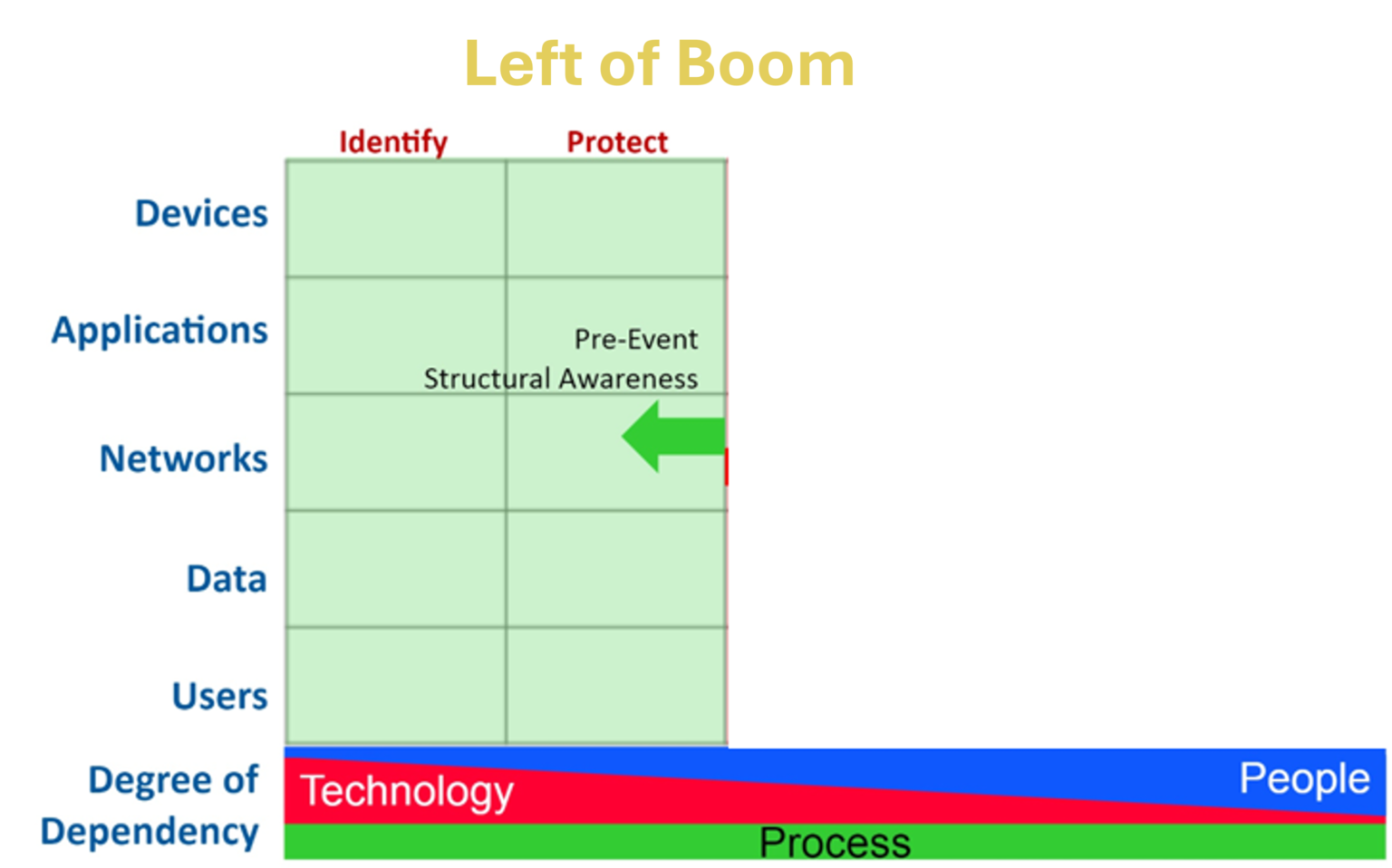
Left of Boom = Prevention and Preparedness
Actions taken before an attack occurs.
Examples include:
- Implementing security controls and best practices.
- Conducting vulnerability assessments.
- Educating employees about security awareness.
- Regularly updating software and patching vulnerabilities
Right of Boom = Prevention and Preparedness
Actions taken after an attack occurs.
Examples include:
- Investigating the breach.
- Containing and mitigating damage.
- Restoring affected systems.
- Communicating with stakeholders